Biometric security: Defending against attacks in iris recognition

It’s a scene straight out of a spy movie: pressing one’s eye right up to a scanner to gain exclusive access to a high-security location.
“It’s a very Hollywood-ish thing, but my team has demonstrated in the past that dead eyes can be used for recognition even a few weeks post-mortem, so developing appropriate countermeasures is a must,” says Adam Czajka, assistant professor in Notre Dame’s Department of Computer Science and Engineering.
Iris recognition is a form of biometric identification technology, which uses iris patterns to recognize individuals. Other popular biometric characteristics used to keep a location or device at maximum security include fingerprints, facial features, and voices.
However, iris recognition only works well when it can defend against attackers using fake objects. While algorithms have been developed to identify previously known attacks, such as printouts of false irises or cosmetic contact lenses, many systems still are defenseless against unknown objects. These attack strategies are called presentation attacks, as the attacker presents a false biometric characteristic to be identified. Czajka recently collaborated with Domingo Mery, full professor in the Department of Computer Science at Universidad Católica de Chile (PUC|Chile), to find solutions to the problem of detecting unknown types of biometric attacks.
“Professor Mery is a distinguished expert in sparse representation coding – a technique that encodes efficiently salient features present in the training data,” says Czajka. “Currently superseded by neural network-based algorithms, sparse representations may offer compact and representative feature sets for various visual recognition tasks. I was delighted by Prof. Mery’s positive response about joining this project, as this expertise was exactly what was needed to make this research successful.”
Czajka has spent 15 years researching and creating solutions for this problem. Iris recognition is a key identifier in important places with high security needs, which only increases its appeal to potential attackers.
“If you have something that is accurate and fast, then, of course, it is exposed more to attacks,” Czajka adds.
His partnership with Mery was made possible through the Luksic Family Collaboration Grant, which seeks to encourage collaborations between Notre Dame faculty and colleagues from PUC|Chile.
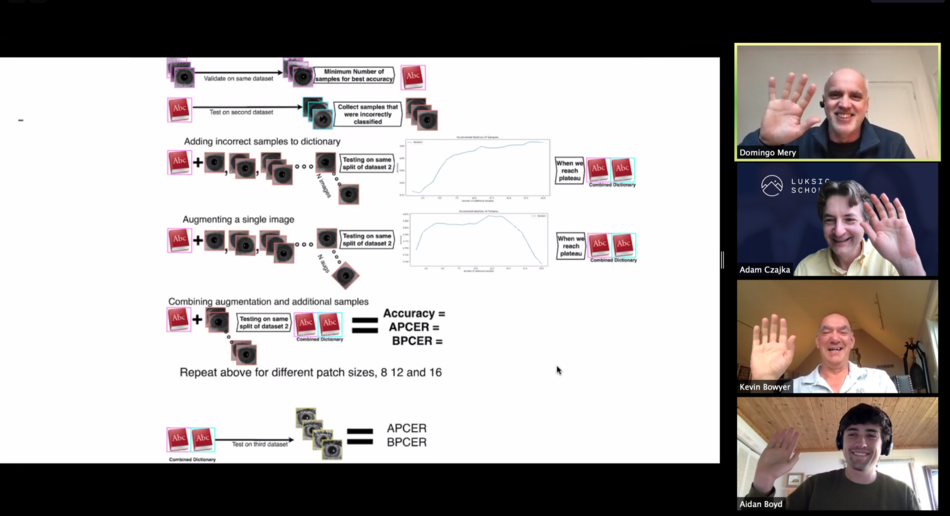
Through this collaboration, Czajka and Mery were able to create an algorithm that can effectively adapt to unknown false iris images, and they plan to continue their work together. They have discussed technical ways to modify the program and know how they can extend their work.
“It has been a very enriching experience,” Mery says. “Having spent my sabbatical year at the University of Notre Dame in 2014-2015, and having worked closely with Professor Czajka during that period, it has been great to work with him again on a new project. Thanks to his graduate student Aidan Boyd, who improved and adapted an algorithm initially developed for face recognition, we have obtained very good results in iris recognition that are about to be published.”
As for the greater Notre Dame community, Czajka sees the importance of bringing awareness to the availability of international partnerships.
“I’m not sure how many people at Notre Dame are aware that they can ask not only for money but to facilitate this kind of collaboration,” he says.
Learn more about the Luksic Family Collaboration Grant.